DevSecOps tools help teams embed security into software delivery without slowing down development. The strongest toolchains combine code analysis, dependency scanning, container security, secrets detection, policy enforcement, and runtime visibility so teams can catch risk earlier and respond faster. If your priority is shifting security left, Kiuwan is a strong option for SAST-driven secure development, while tools like GitLab, Snyk, Aqua, Checkmarx, and SonarQube can fill other parts of the DevSecOps stack.
DevSecOps tools form the backbone of modern secure software delivery. As organizations race to release features faster, the challenge is not just writing great code. It is also making sure every commit, container, and deployment is protected against evolving threats.
That is where DevSecOps comes in, weaving security into every stage of the development lifecycle without forcing teams to choose between speed and safety. The right tools help developers catch vulnerabilities early, automate policy checks, and build more secure software with less rework.
In this post, we will cover the main categories of DevSecOps tools, explore the top platforms teams rely on, and share practical guidance on how to choose the right toolchain for your organization.
The rise of cloud-native applications, microservices, and continuous delivery pipelines has reshaped how software is built and released.
But with faster delivery comes greater risk. Security vulnerabilities can reach production long before traditional reviews or audits catch them. DevSecOps tools help address this by embedding security checks directly into the development process, so teams can identify and fix issues earlier.
Instead of treating security as a final checkpoint, DevSecOps brings it into daily workflows. Tools for static application security testing (SAST), dependency scanning, container scanning, secrets detection, and policy enforcement help teams work more securely without adding unnecessary friction. This reduces costly rework and helps organizations support internal security standards and external compliance requirements.
Most importantly, DevSecOps tools enable closer collaboration between development, operations, and security teams. By shifting security left and automating protections where possible, organizations can release software faster while improving resilience across the pipeline.
DevSecOps tools span multiple categories, each addressing different risks in the software development lifecycle. Below are the most common types and the roles they play in strengthening application security.
Runtime security and monitoring: provides visibility into production environments and helps detect threats in real time
| Category | Primary function |
| Static application security testing (SAST) | Scans source code during development to detect vulnerabilities early. |
| Dynamic application security testing (DAST) | Tests running applications to uncover runtime and input-validation issues. |
| Software composition analysis (SCA) | Flags vulnerabilities in open-source libraries and third-party components. |
| Container and image scanning | Identifies vulnerabilities and misconfigurations in containerized workloads. |
| Secrets detection | Prevents credential leaks by scanning repositories for keys, tokens, and passwords. |
| Policy enforcement and compliance | Helps align toolchains with standards such as PCI DSS, HIPAA, and GDPR. |
| Runtime security and monitoring | Provides continuous monitoring and threat detection in production environments. |
Below are some of the leading DevSecOps tools organizations rely on today. Each plays a different role in securing code, dependencies, containers, and production environments, helping teams shift security left without slowing delivery.
Overview:
Kiuwan helps teams shift security left with SAST, code quality analysis, and software composition analysis through its Code Security and Insights products. It supports 30+ languages, integrates with popular IDEs and development environments, and maps findings to standards such as OWASP, CWE, PCI, CERT, and SANS. It is available in hybrid-cloud and on-premises deployment models, which makes it a strong fit for teams that want flexible, secure-by-design adoption.
Pros:
Cons:
G2 score: ★★★★☆ (4.5/5)
Overview:
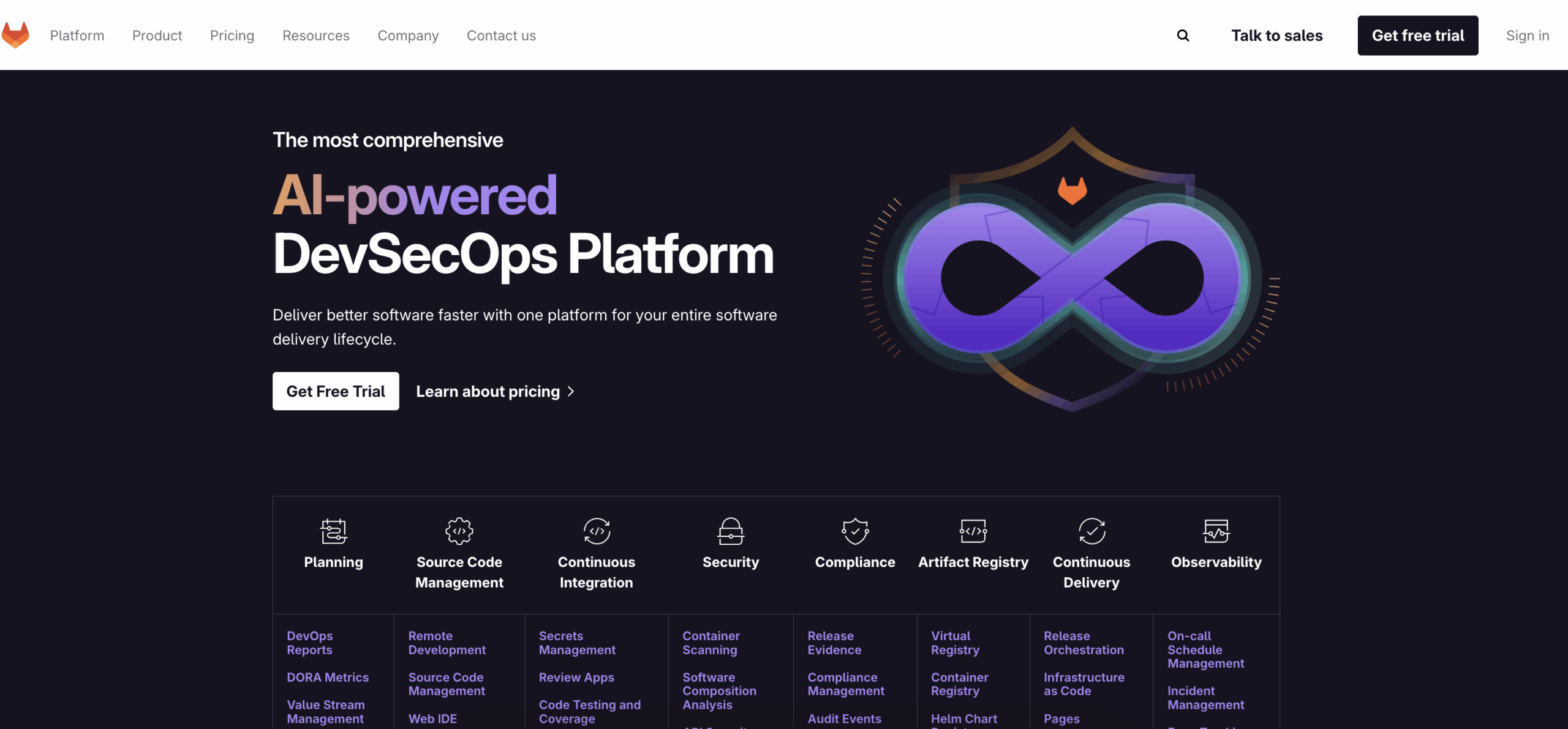
GitLab provides an integrated DevSecOps platform with built-in support for SAST, DAST, dependency scanning, and secret detection. Its security features plug directly into GitLab CI/CD and merge request workflows, making it a strong option for teams that want centralized delivery and security in the same platform. GitLab also supports diff-based and advanced SAST workflows for supported languages.
Pros:
Cons:
G2 score: ★★★★☆ (4.5/5)

Overview:
Snyk is especially strong in software composition analysis, while also covering SAST, container security, and infrastructure as code security. Its developer-first approach, IDE and repo integrations, and in-workflow remediation guidance make it a popular choice for teams that want to address open-source and cloud-native risk early.
Pros:
Cons:
G2 score: ★★★★☆ (4.5/5)
Overview:
Aqua Security focuses on cloud-native security across containers, Kubernetes, serverless, and runtime environments. Its platform emphasizes image scanning, runtime protection, compliance support, and contextual prioritization to help teams reduce noise and focus on the risks that matter most in production.
Pros:
Cons:
G2 score: ★★★★☆ (4.2/5)
Overview:
Checkmarx is a long-established AppSec platform with strong enterprise support across SAST and related application security capabilities. Its current platform messaging emphasizes SAST, SCA, API security, secrets detection, IaC security, and container security, along with features such as Fast Scan, Best Fix Location, and AI Query Builder for customizing queries.
Pros:
Cons:
G2 score: ★★★★☆ (4.2/5)
Overview:
SonarQube combines static analysis for code quality and security, making it a strong fit for teams that want to improve maintainability and catch vulnerabilities within the same workflow. SonarQube currently supports 30+ languages, frameworks, and IaC platforms, and recent Sonar materials highlight AI CodeFix and AI Code Assurance capabilities.
Pros:
Cons:
G2 score: ★★★★☆ (4.4/5)
| Tool | Best for | Primary strengths | G2 Score |
| Kiuwan | Static application security testing (SAST) | Broad language support, CI/CD and IDE integration, standards-based reporting, flexible deployment | 4.5/5 |
| GitLab | Integrated DevSecOps pipelines | All-in-one platform with built-in SAST, DAST, dependency scanning, and secret detection | 4.5/5 |
| Snyk | Software composition analysis (SCA) | Strong open-source risk detection, developer-first integrations, cloud-native security coverage | 4.5/5 |
| Aqua Security | Container and cloud-native security | Container and Kubernetes protection, runtime visibility, compliance support | 4.2/5 |
| Checkmarx | Enterprise-scale application security | Broad AppSec coverage, scalable enterprise workflows, detailed remediation support | 4.2/5 |
| SonarQube | Code quality and maintainability with security checks | Combines code quality and security checks, strong developer workflow support | 4.4/5 |
With so many DevSecOps tools available, the best approach is not to adopt everything. It is to choose the right combination for your team’s workflows, risk profile, and delivery model. The strongest toolchains balance developer experience with security depth and operational clarity.
When evaluating options, consider the following:
For teams focused on shifting security left, Kiuwan’s customizable analysis, broad language support, and flexible deployment model make it a strong foundation for secure development. Paired with complementary tools for container security, dependency scanning, and runtime monitoring, it can help organizations build a more secure and resilient DevSecOps workflow.
Ready to strengthen your pipelines and catch vulnerabilities earlier? Start a free Kiuwan trial today!
DevSecOps tools are technologies that embed security into the software development lifecycle. They automate activities such as code scanning, dependency analysis, secrets detection, container security, and runtime monitoring so teams can identify risk earlier and respond faster.
They help teams catch vulnerabilities before release, reduce manual security bottlenecks, and make security part of everyday development instead of a final-stage review. That usually means faster remediation, less rework, and stronger overall software delivery.
Widely used options include Kiuwan for SAST for integrated DevSecOps workflows, Snyk for software composition analysis and developer-first security, Aqua Security for cloud-native and container security, Checkmarx for enterprise application security, and SonarQube for code quality with security checks.
Most modern DevSecOps tools connect directly to CI/CD workflows so scans can run automatically during builds, pull requests, or deployments. This helps teams surface security findings earlier without adding a separate manual process.
Look for strong workflow integration, broad coverage across the lifecycle, actionable remediation guidance, prioritization that reduces alert noise, and the ability to scale as your application portfolio grows.
Not exactly. AppSec tools focus specifically on securing applications, while DevSecOps tools support a broader pipeline-level approach that can include code, dependencies, infrastructure, containers, and runtime environments. AppSec is part of DevSecOps, but it is not the whole picture.
No. Smaller teams can benefit from lightweight or focused tools, while larger enterprises often build broader toolchains with more governance, reporting, and policy controls. The right choice depends more on complexity and risk than on company size alone.
No. They work best alongside activities such as manual review, penetration testing, and architecture assessments. DevSecOps tools provide continuous automated coverage, while traditional testing can validate bigger or more targeted risks.
If your main goal is early code-level detection inside developer workflows, Kiuwan is a strong choice because it focuses on SAST-driven secure development, supports 30+ languages, and offers flexible deployment and standards-based reporting.